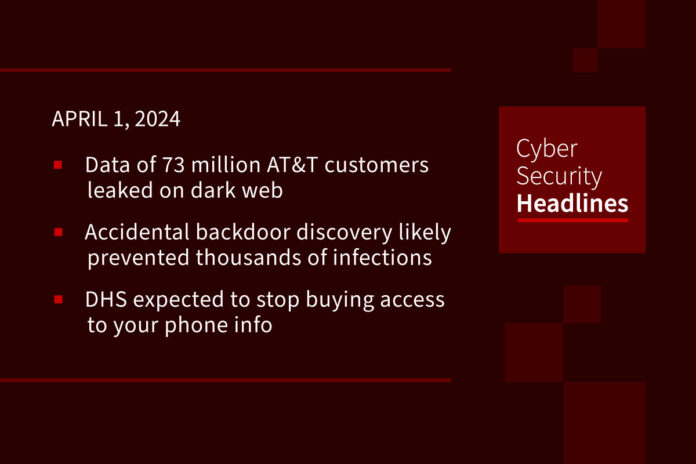
Data of 73 million AT&T customers leaked on dark web
On Saturday, AT&T said that data on roughly 73 million current and former customers was exposed on the dark web, including social security numbers and other personal information. The data appears to be from 2019 or earlier. Interestingly, AT&T disclosed the news on Easter holiday weekend, though data that surfaced on the dark web roughly two weeks ago. AT&T said a “robust investigation” is underway but so far they have no evidence of unauthorized access to their systems.
Accidental Linux backdoor discovery likely prevented thousands of infections
On Friday, Red Hat issued an urgent security advisory that Linux users should immediately stop using Fedora 41 or Fedora Rawhide. Red Hat said these Linux distributions contain a 10.0 CVSS severity backdoor vulnerability (CVE-2024-3094) in XZ Utils, the XZ format compression utility. The backdoor was slowly introduced through updates by the alias “Jia Tan”, which is likely not a real name and possibly a group of individuals or even a nation state. A developer named Andres Freund discovered the stealthy backdoor by accident after noticing some odd ssh performance issues and valgrind crashes. Some are saying Freund’s discovery could potentially prevent thousands of infections. The US Cybersecurity and Infrastructure Security Agency (CISA) has advised XZ Utils users to downgrade to an earlier, uncompromised version and hunt for any malicious activity.
(The Hacker News and Dark Reading and The Record and Security Boulevard)
DHS expected to stop buying access to your phone info
Since 2018, Department of Homeland Security (DHS) agencies, including Immigration and Customs Enforcement, U.S. Customs and Border Protection and the U.S. Secret Service, have been buying access to commercially available data revealing the location of devices, many inside the United States. Commercially available phone data can be bought and searched without judicial oversight. The data has been used to crack down on border crossings, identify human trafficking, locate undocumented immigrants, and for criminal investigations. Sources are now saying that DHS is expected to discontinue purchasing device data in the face of pending recommendations from the DHS inspector general that the agency enact stronger privacy controls and policies.
(NOTUS)
Vultur banking malware poses as McAfee security app
Security researchers have found a new version of the Vultur banking trojan for Android. The initial version was discovered in March 2021 and was being distributed through dropper apps on Google Play. The new version of Vultur masquerades as a McAfee Security app that threat actors are tricking victims into installing through smishing (SMS phishing) and vishing (phone calls) attacks. The new malware has improved remote control over infected devices with commands for scrolling, swipe gestures, clicks, volume control, and blocking apps from running. The malware also better evades detection by encrypting command-and-control (C2) communications. To minimize the risk of infection, users are urged to only download apps only from reputable repositories and avoid clicking on URLs in messages.
Huge thanks to our sponsor, Vanta

To learn more, go to vanta.com/ciso.
Activision urges users to secure stolen accounts with 2FA
A Discord user discovered an infostealer database that targeted users of a service…
This article was originally published by a cisoseries.com . Read the Original article here. .